Securing your WordPress wp-config.php file is one way to beef up your WordPress security. It is one of the most important WordPress files and contains very sensitive information about your WordPress installation, such as the WordPress security keys and the WordPress database connection details, among many other configurations. You certainly do not want the content of this file to fall into the wrong hands. Taking steps to protect the WordPress wp-config.php file is definitely something you should take seriously.
In this tutorial, we will explain how to protect this important WordPress configuration file and how to store the sensitive information in the wp config.php file somewhere secure and not accessible via the web.
Why is wp-config.php security important?
This file contains information to help you establish a database connection. It contains MySQL settings including the database name, database username, database password, and database hostname. WordPress relies on these four values to connect to the right MySQL database.
The wp-config.php file also contains WordPress security keys and salts that it uses to make storage of information related to user sessions, passwords, and any other sensitive data more secure. For example, WordPress doesn’t store actual user passwords in the database in plain form. It creates one-way hashes of those passwords and then stores the hashes. The salts simply provide additional randomness that WordPress can use to make it even harder for malicious users to crack your passwords.
They also help in authentication when someone tries to access your website. Once a user submits their username and password for login, WordPress will use the salts configured in the wp-config.php file to recalculate the hashes and determine if the user should be allowed access.
The file has configuration options for a variety of other purposes, such as moving the plugins, uploads, or wp-content folder. You can also use it to specify an autosave interval and the number of post revisions that WordPress should save, if any at all.
How to access the wp-config.php file
The wp-config.php file isn’t initially present in the package that you download to install WordPress. It is created during the installation process.
When you are setting up a WordPress site, the installer will ask you to provide details like the database name, database username, database password, database hostname, etc. WordPress then creates the wp-config.php file based on the data that you feed to it.
The default location of this file is inside the root directory where you are installing WordPress. You can easily access it either through the file manager in your cPanel account or through an FTP client. You’ll need to ensure you have the FTP credentials to connect via this method. Another way to access the file would be through SSH. You’ll need to make sure you have your SSH login credentials before accessing the file.
Unless you installed WordPress in a sub-directory, the wp-config.php file will be inside the WordPress root folder. Typically, this is either the public_html or www folder. Some web hosts may also set up their servers to place the wp-config.php file up one directory level to improve security. Make sure you check for the file there if you can’t find it in the root directory.
WordPress is able to load the file automatically if it is located either in the root directory or one level up. We will discuss this in detail later in the tutorial.
How to edit the wp-config.php file
As we progress in this tutorial, you might need to download your wp-config.php file and upload it back up after making relevant changes. Downloading the file isn’t always necessary. You can also edit it directly after connecting via SSH and using an editor like nano or vim.
You can easily open and edit the file using simple text editors like Notepad. However, we recommend that you use some more capable applications, such as Notepad++ or Visual Studio Code, since these editors provide syntax highlighting. As the wp config file is a php file, editing it becomes less error-prone if you are using an editor that supports syntax highlighting.
Securing the wp-config.php file
As we saw in the previous section, the wp-config.php file is critical for a functioning WordPress website. It contains a lot of sensitive information that has to be kept secure at all costs to maintain site security.
We will now discuss four different techniques that you can use to protect this important file from unauthorized access.
Block access to the wp-config.php file using .htaccess
WordPress usually adds an .htaccess file to the root installation directory of your website. This file can serve a lot of functions, such as URL redirects, error handling, caching and compression, and access control.
Here, we are interested in restricting access to the wp-config.php file through the .htaccess file located in the root directory of your WordPress installation. Open the .htaccess file in an editor of your choice and then add the following directive to it:
<Files wp-config\.php>
order allow,deny
deny from all
</Files>There are two important points that you have to keep in mind while trying to restrict access to wp-config.php files using .htaccess directives:
- The .htaccess file and the wp-config.php file need to be in the same directory. The wp-config.php file is in the root directory of your WordPress installation. Therefore, you need to create a new .htaccess file in the root directory as well if it doesn’t already exist.
- There is a chance that your WordPress installation might have an existing .htaccess file. In this case, you need to make sure that you don’t place the blocking directives within the # BEGIN WordPress and # End WordPress blocks. This is because any rules that you place within these blocks might get overwritten in the future.
Moving or relocating the wp-config.php file
The wp-config.php file resides inside the root folder of your WordPress installation by default. Many bad actors will also expect this file to be present there. However, you can make the file harder to locate by moving the file to a different location.
Make sure you have a backup of your WordPress website before proceeding. This is important as we will be making changes to some of the core files.
How WordPress finds the wp-config.php file
We will now look at the migration steps for the wp-config.php file. It helps to be familiar with the way WordPress loads the file.
The root directory contains a bunch of important core WordPress files. One of those files is index.php. This index.php file is different from the index.php file of the theme installed on your WordPress website.
The sole purpose of the index.php file is to load the wp-blog-header.php file using the following line:
require DIR . '/wp-blog-header.php';The wp-blog-header.php file is also located in the root directory. This is the file responsible for loading the wp-load.php file. It does so inside an if block which also sets the value of the $wp_did_header variable. The true value lets different functions and filters know that WordPress has already sent headers as shown by the following lines:
if ( ! isset( $wp_did_header ) ) {
$wp_did_header = true;
// Load the WordPress library.
require_once DIR . '/wp-load.php';
// Set up the WordPress query.
wp();
// Load the theme template.
require_once ABSPATH . WPINC . '/template-loader.php';
}Once the wp-load.php file loads, it executes the code to load the wp-config.php file. There are three blocks here to handle different situations.
if ( file_exists( ABSPATH . 'wp-config.php' ) ) {
require_once ABSPATH . 'wp-config.php';
} elseif ( @file_exists( dirname( ABSPATH ) . '/wp-config.php' ) && ! @file_exists( dirname( ABSPATH ) . '/wp-settings.php' ) ) {
require_once dirname( ABSPATH ) . '/wp-config.php';
} else {
// More Code to initiate the setup process.
}The if block checks if the file is present inside the root WordPress directory. This is usually the case with a default WordPress installation. In this situation, WordPress will load the wp-config.php file from the root directory.
Let’s say the file wasn’t present in the root directory. In this case, WordPress moves to the elseif block which checks if the file is actually located one level up or in the parent directory. It also performs an additional check to see if there is a wp-settings.php file in the parent directory. The presence of a wp-settings.php file in the parent directory indicates a nested installation.
If there is no wp-settings.php file in the parent directory, WordPress loads the wp-config.php file of that directory.
The code inside this elseif block allows you to simply move and load your wp-config.php file from up one directory without ever worrying about making any changes to the code.
If the parent directory isn’t a publicly accessible folder, this check provides an easy way of improving your WordPress security. You won’t have to make any changes to the code. WordPress will automatically find the wp-config.php file that is only one level above the root installation directory.
If WordPress can’t find the wp-config.php file in either of these locations, it will start the loading the setup process. This will result in creation of a new wp-config.php file. Therefore, it is important that WordPress finds and properly loads your desired configuration file.
Remove sensitive information from the wp-config.php file
When we talk about protecting the wp-config.php file from attackers, our aim is to simply keep the sensitive information inside the file secure.
Another option that keeps the sensitive information safe involves moving just the sensitive information while keeping the wp-config.php file in its original location. You can also just move the sensitive information like the database connection details, and the salts and keys to a different location.
Step-by-step guide
Let’s walk through the process step-by-step:
- Just like the previous technique, begin by creating a new directory above the public_html or www folders so that it stays out of reach for website visitors. It would be great if the name of the directory does not indicate that you are using it to store information from the wp-config.php file. For example, a directory name like nkm-cache doesn’t raise suspicions that you are using it to store something important.
- Create a new file within the nkm-cache directory and give it a random name like image-thumbs.php.
- Copy all the sensitive information that you want to hide from wp-config.php and place it inside the new file you just created.
- Add a reference to the newly created file inside your original wp-config.php file by including the line below inside your wp-config.php file. The first two lines of your wp-config.php file should now look like this:
<?php
require_once ('/home/username/nkm-cache/image-thumbs.php');Make sure you change the path according to your own server configuration. You will most likely get HTTP 500 server errors if the path doesn’t match the location of the file.
If you aren’t sure what the right path for the file would be, you can use your FTP application or the file manager in control panels like cPanel. Consider the following screenshot:
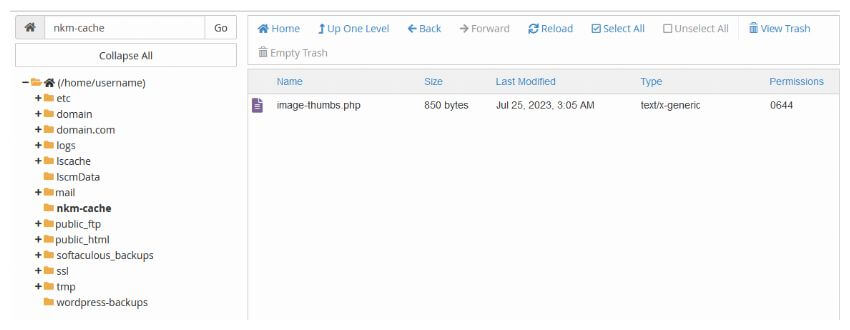
The path besides the home icon, i.e., /home/username/ is your root directory. The bold directory is the current selected directory. Join all these together along with the file name using a forward slash and you have got the path that you need to supply inside the wp-config.php file. In this particular case, the current selected directory is nkm-cache, the image file is image-thumbs.php. Therefore, the full path will be:
/home/username/nkm-cache/image-thumbs.php
Choose proper file permissions
We have already discussed the role of file permissions in protecting WordPress files.
One thing worth considering, is updating the permissions of all files and directories where you are storing sensitive information. For example, if you created a new file to store the sensitive data from the wp-config.php file, make sure that the new file has 644 as permission.
Be mindful of backups
It is good practice to take a backup of any file you’re about to edit. Doing so allows you to revert back quickly should something go wrong. This procedure also applies when it comes to editing WordPress configuration files, including wp-config.php. These backups are typically separate to WordPress backups.
It remains important, however, to ensure that any file backups you take do not end up as unreferenced or exposed files on your WordPress server. Failure to do so can result in sensitive information such as your mySQL database password or WordPress security keys being leaked online.
You might also want to use Website File Changes Monitor to keep tabs on WordPress files and folder changes.
Final thoughts
The wp-config.php file is an integral part of your website. Keeping the information inside it safe is vital for improving your website security and preventing data breaches.
Keep in mind moving the wp-config.php file outside publicly accessible directories isn’t an ultimate solution for improving WordPress security. It just provides an additional layer of security in situations where a misconfigured web server starts spitting out plain text instead of processed PHP web pages.